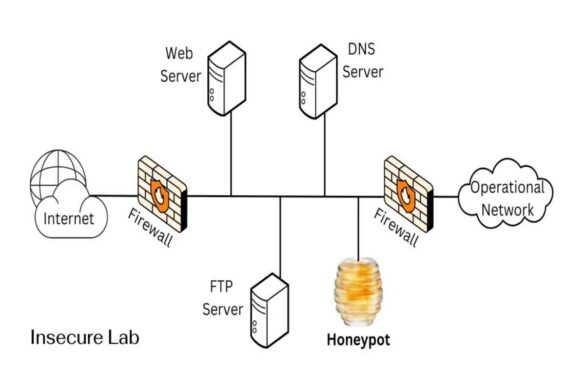
What is Honeypot in Cyber Security
Online security within organisations should be the top-most priority to protect sensitive data. Due to this, cybersecurity is becoming essential…
Ensuring Data Security During Cloud Migrations
As companies increasingly shift their essential systems and data to the cloud, the safety of these assets during the transition…
A Teen’s Guide to Navigating the Perils of Online Interaction on Social Media
Perils of Online Interaction In the digital age, social media has become an integral part of a teenager’s life, offering…
What’s the Significance of a Security Risk Assessment?
Security risk assessment is an essential component of cyber security operations since it protects the company from intrusions, attackers, and…
Cybersecurity: It’s not as difficult as you think
The computer and internet industry has grown exponentially over the last two decades, significantly increasing the career opportunities that the…